Hello Community
My question is this, I have a UTM 9 Sophos, in one of our interfaces have public IP 190.25.189.210 which we are listing on blacklists.
When I go to check indicates CBL page the following message:
This IP address is infected with, or is NATting for a machine infected with Palevo (Microsoft).
Palevo (also known as Rimecud, Butterfly bot and Pilleuz) is a worm that spreads using instant messaging, P2P networks and removable drives (like USB sticks).
The CBL detection is being made using sinkholing techniques.
Further (technical) information about Palevo can be obtained here:
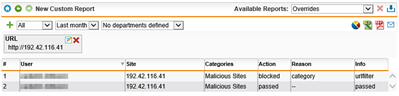
This was detected by a UDP connection from 190.25.189.210 on port 2963 going to IP address 192.42.116.41 (the sinkhole) on port 50000.
The botnet command and control domain for this connection was "".
Behind a NAT, you should be able to find the infected machine by looking for attempted connections to IP address 192.42.116.41 or host name on any port with a network sniffer such as wireshark. Equivalently, you can examine your DNS server or proxy server logs to references to 192.42.116.41 or . See Advanced Techniques for more detail on how to use wireshark - ignore the references to port 25/SMTP traffic - the identifying activity is NOT on port 25.
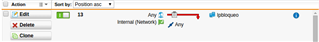
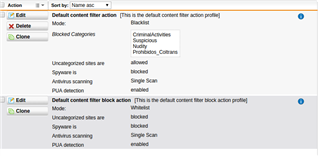
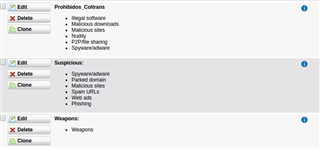
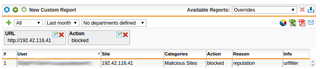
I have a rule that denies all traffic from that network segment and yet I still blocking've reviewed all policies and we found our UTM which is the gap.
I need help.
This thread was automatically locked due to age.