Hello!
Is anyone aware of any danger of having the same user logged into multiple computers at the same time when implementing Heartbeat Authentication and NTLM?
Take this as an example;
We have 2 computers and one Sophos XG. All setup with SSO to an Active Directory which works perfectly fine.
We have 2 authentication servers on the Sophos XG to two separate AD's. This is because we utilize two UPN's in our domain, so some users have a UPN of "@CompanyOne.com" and some users have a UPN of "@CompanyTwo.com".
Both of these computers have Sophos AV installed and both of the computers, when logged into - appear on the Sophos XG with the correct UPN and the correct authentication method "Heartbeat". It should be known at this point, NTLM authentication or better known in Version 18 as "AD SSO" is enabled and used as a fallback when heartbeat has a problem or the client doesn't have Sophos AV.
My issue is this;
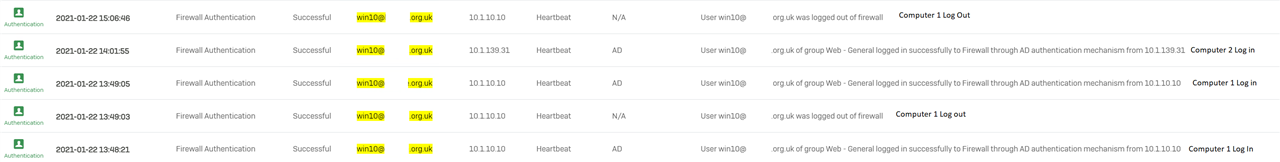
Computer 1 logs in at 09:30 AM. They login as "User1@companyone.com" and this appears on authentication as "heartbeat" with the Sophos XG.
Computer 1 continues to browse, listen to internet radio and generally "do stuff" until 10:30 AM. They go and make a cup of tea.
Computer 2 logs in at 10:35 AM. They login as "User1@companyone.com" and this again appears fine on the Sophos XG.
Computer 2 is browsing, having a whale of a time.
Computer 1, the user returns to the workstation and find his internet radio stream has stopped. He loads up "bleepingcomputer.com" and find they are redirected for ntlmauth.
The Sophos XG logs, at the time of the problem shows that the client should be authenticated. But the issue occurs after a login on Computer 2.
I can't find any documentation to state there is a limitation on how many PC's a single user can login to.
And on the other hand, there was a bug in SFOS 17.5.7 where a user will be prompted for NTLM when they're actively logged in using Heartbeat - this was patched in SFOS 17.5.9. We're now on 18.0.4. We've been assured in the past that bugs do not return in later Firmware versions by Sophos rep's because of the testing procedure they use in house. So is there an issue with my setup?
This thread was automatically locked due to age.


